Email Security Protocols: Your Defense Against Online Threats
Implementing email security protocols can significantly reduce the risk of email spoofing and phishing attacks.
Campaign Refinery Team
Email Marketing Experts
What you'll learn
Today, when most human interactions happen via electronic means, email security protocols are necessary.
The internet has undergone a remarkable transformation in the last two decades; it has evolved from a novel technological curiosity into an integral part of our daily lives. And in this world of digital messaging, email reigns supreme.
The stats back it up; the number of emails sent daily has gone from 12 billion emails in 2000 to 347 billion emails in 2023.
However, as technology brings the world closer, there are also many security issues we have to be aware of. For example, phishing emails or email spoofing are more prevalent than ever before — Google blocks over 100 million phishing emails every day.
This is why we need email security protocols; they ensure our private and sensitive information remains confidential and secure. The most critical reason, however, is that your email deliverability will suffer without these email security requirements. Without them, you’ll often wonder why your emails go to spam.
Let’s dive into the world of secure email protocols and learn how to prevent email threats.
What are Email Security Protocols?
Email security protocols are a set of standardized rules and practices designed to enhance the security of email communications via email authentication.
These protocols include measures to encrypt email messages, verify the identity of senders and recipients, prevent spam and phishing attacks, and protect against threats related to email security.
What Security Protocols are Used to Protect Email?
Email security and privacy rely primarily on TLS encryption for protecting messages in transit between email servers and clients.
Common authentication protocols such as SPF, DKIM, and DMARC help verify sender identity and prevent spoofing. End-to-end encryption protocols such as PGP and S/MIME provide additional security by encrypting the actual message content so only intended recipients can read it.
List of Email Security Protocols
Common email security standards include:
| Email security protocols | Full form |
|---|---|
| SSL in email or TLS | Secure Sockets Layer or Transport Layer Security |
| SPF | Sender Policy Framework |
| DKIM | DomainKeys Identified Mail |
| DMARC | Domain-based Message Authentication, Reporting, and Conformance |
| BIMI | Brand Indicators for Message Identification |
| PGP | Pretty Good Privacy |
| S/MIME | Secure/Multipurpose Internet Mail Extensions |
Besides the above list of email protocols, there are anti-malware and anti-phishing spam filters to safeguard against malicious attachments and links. These protocols collectively work to make emails safer against the types of email threats mentioned in the section below.
Common Email Security Threats
Email protocols safeguard against different types of email security threats, such as:
- Phishing attacks: These target specific individuals with fraudulent messages.
- Business Email Compromise (BEC): This involves impersonation of executives or trusted partners.
- Malware and ransomware: These are malicious files delivered through attachments or links.
- Man-in-the-middle attacks: These attacks involve the interception of unencrypted email communications.
- Spoofing: This is an email security threat that occurs when a malicious user sends an email pretending to be a trusted acquaintance.
- Password spraying and brute force attacks: These attacks rapidly use a range of characters to get past security on email accounts.
- Data exfiltration: This method involves using compromised email accounts.
- Zero-day exploits: These are software scripts that target email client vulnerabilities.
You can greatly reduce these email security risks by embracing email security standards — read on to understand the full scope of the benefits.
The Benefits of Email Security Protocols
Imagine a world without security protocols; anyone could access your emails and steal your data. Email security protocols play a vital role in reducing threats via email.
Let’s review the benefits of having these protocols in place:
- Confidentiality: Communication encryption protocols, such as TLS, help maintain the privacy of your email content, preventing unauthorized access and eavesdropping.
- Authentication: Protocols like SPF, DKIM, and DMARC help verify your authenticity, boosting your email sender reputation. It’s also a mandate in the Yahoo and Gmail spam update.
- Integrity: Your recipient can be sure the message they received is identical to the one you sent, guaranteeing data integrity.
- Protection against spyware/malware: Security protocols include anti-malware filters, which help block malicious links or email attachments in marketing that can introduce malware into a system.
- Reduced spam: These protocols tell mailbox providers that you are not a spam email sender.
- Compliance: Email security protocols on your email domain are necessary to meet regulatory and compliance rules outlined in the GDPR compliance checklist or CAN-SPAM requirements.
- Prevention of phishing scams: Security protocols make it more challenging for cybercriminals to pretend to be you; this reduces the risk of your email marketing subscribers falling for scams.
Email Security Protocols in Cyber Security
As remote work becomes standard and email gets more critical for business operations, robust email security is vital. It has evolved from a technical requirement to an essential business continuity measure.
Email security protocols have become fundamental to protecting organizations from data breaches, phishing attacks, and financial fraud. In 2025, companies must invest in cybersecurity and implement authentication standards to prevent email spoofing. They must also apply encryption protocols to safeguard sensitive data both in transit and at rest.
Now that we are aware of the critical role email security protocols play, let’s learn more about the common ones in use today.
The Importance of Security Protocols in Email Marketing
In email marketing, where the trust of your recipient is paramount, every email security standard is crucial. This is because marketing emails are a lot less personal than workplace or personal emails. It would annoy subscribers to receive an email that poses a security threat to them.
But there’s more to it.
Let’s examine why you need to take secure email protocols seriously as an email marketer.
- Email delivery: Implementing email security protocols helps ensure your messages reach inboxes; save yourself the trouble of figuring out how to remove email from a spam list.
- Maintaining deliverability: High deliverability rates are crucial for successful email marketing. Implementing security protocols helps improve email deliverability rates by ensuring your messages reach your readers. This also helps increase email open rates.
- Sender authentication: These protocols are good for email engagement.
- Data security: Email marketing often involves the collection of customer data. Implementing secure email protocols helps protect and safely transmit this sensitive information.
- Tackle phishing risks: Different types of email campaigns can be targets for phishing attacks if not properly secured.
- Compliance: Different email protocols are necessary to comply with data protection and privacy regulations. Ensuring compliance is essential to avoid legal issues.
As part of email best practices, we recommend you add security protocols to both your domain and website.
Protect Your Brand Image With Different Types of Email Protocols
Secure emails contribute to a positive brand reputation. Protecting your company’s image is essential in email marketing because it can impact the success of your campaigns and how recipients perceive your business.
Secure email communications also help build trust with your customers. When they receive well-authenticated emails, they are more likely to trust your company.
Security Protocols List for Email Marketing
To be successful with email marketing, you must know all about these protocols for email:
- SSL or TLS,
- SPF,
- DKIM,
- DMARC,
- BIMI,
- PGP,
- S/MIME.
After this section, we do a deep dive into all the protocols on this list, starting with SSL.
SSL is an Essential Email Security Protocol
SSL, or TLS as it is known today, plays a crucial role in securing email communication, just as it does for web browsing. In the context of email, TLS provides encryption and offers secure transmission of email messages between clients and servers.
Check out the different ways TLS helps your emails reach their destination safely:
- Encryption: TLS encrypts the content of your email messages as they travel between email clients and servers.
- Authentication: When two email servers communicate using TLS, they can verify each other’s identities. This helps prevent security threats such as email spoofing and man-in-the-middle attacks.
- Secure connections: TLS establishes secure connections between email clients (like Outlook or Thunderbird) and email servers (for example, Gmail or MS Exchange). This ensures protection against eavesdropping and tampering.
- Protection during email relay: Email messages often travel through multiple email servers; TLS can ensure the message remains encrypted and secure throughout its journey.
- Compliance and regulatory requirements: Many regulations and data protection standards, such as the General Data Protection Regulation (GDPR) and CAN-SPAM, require the use of TLS.
TLS can be classified into two types — read on to learn the differences.
Opportunistic TLS vs Forced TLS
The two types of TLS are opportunistic TLS and forced TLS.
- Opportunistic TLS: This version of TLS encrypts communication between two parties whenever possible, without strict requirements. If both the sender and recipient support TLS encryption, they will use it to secure their communication. However, if one party doesn’t support TLS, the communication may continue without encryption.
- Forced TLS: This is a stricter approach; when using forced TLS, one party, typically the sending server, mandates using TLS encryption for communication, and the other party must comply. If the recipient’s server doesn’t support TLS, it rejects the communication.
This table highlights the differences between the two:
| Feature | Opportunistic TLS | Forced TLS |
|---|---|---|
| Encryption | Optional: It encrypts when both sender and recipient support TLS. | Mandatory: It requires encryption for all communication. |
| Security leniency | Opportunistic TLS is less strict, allowing unencrypted communication if the other party doesn’t support TLS. | Forced TLS is strict, enforcing encryption for communication. |
| Compatibility | It is compatible with a broader range of email systems, as it doesn’t force encryption. | It may lead to issues if the recipient’s server doesn’t support TLS. |
| Flexibility | It offers flexibility for cases where immediate encryption isn’t possible. | It provides high-level security but non-delivery is possible if TLS isn’t supported. |
| Use cases | It’s suitable for situations where universal encryption isn’t feasible or necessary. | It’s ideal for secure environments or scenarios where strict security is essential. |
| Data protection | It provides encryption and security when supported, enhancing security while allowing for flexibility. | It ensures strong encryption for all communication, offering higher security assurance. |
While Forced TLS can seem like the obvious choice, deciding between Opportunistic TLS and Forced TLS depends on specific security requirements and the level of control and assurance needed for a particular email system.
S/MIME is one of the Best Email Encryption Protocols
S/MIME, which stands for “Secure/Multipurpose Internet Mail Extensions,” is a widely used email security protocol that provides cryptographic security for emails. Many email providers use S/MIME to ensure the confidentiality, integrity, and authenticity of email communications.
Here are the features (and benefits) of using S/MIME to protect your emails:
- Email encryption: S/MIME enables the encryption of your email messages and their attachments. This ensures your content is secure and only the intended recipient can access it, preventing eavesdropping by unauthorized parties.
- Digital signatures: S/MIME allows you to apply digital signatures to your email messages. These signatures verify your authenticity and confirm that no one tampered with the email during transit.
- Public Key Infrastructure (PKI): S/MIME relies on PKI technology, which involves the use of public and private keys for encryption and digital signatures. This means you have to use your private key to sign the message, and the recipient uses your public key to verify the signature.
- Compatibility: Various email clients support S/MIME, making it a widely adopted standard. It ensures users of different email services can send and receive secure emails if they both support S/MIME.
- Authentication: S/MIME provides a strong level of authentication, making it challenging for malicious actors to impersonate you or modify the content of your emails.
S/MIME is commonly used in business and corporate email environments, where data security and privacy are of utmost importance. It is an effective solution for safeguarding sensitive and confidential email communications.
PGP and OpenPGP
PGP (Pretty Good Privacy) and OpenPGP are related encryption standards and systems designed for securing email and data communications.
While PGP has a proprietary history, OpenPGP ensures interoperability across a wide range of open-source implementations, with GnuPG being a prime example. OpenPGP has gained trust in the security community for its open, collaborative approach, making it the preferred choice for those seeking secure email and data communication without proprietary constraints.
Learn more about both protocols below.
Pretty Good Privacy (PGP)
The founder of PGP, Phil Zimmermann, originally developed it in 1991 as a proprietary encryption software and protocol. It gained popularity in the early 90s as a security measure for files uploaded to Bulletin Board Systems.
PGP may have waned in popularity over the years but is still used for email encryption, file encryption, and digital signatures. It utilizes a combination of symmetric and asymmetric encryption, along with a web of trust model, to manage encryption keys.
PGP is not open source, which has raised concerns about the ability to inspect the code for vulnerabilities. Various companies have owned PGP since, including PGP Corporation, which Symantec acquired. Despite its proprietary origins, various open-source PGP-compatible tools and implementations were developed, allowing for broader compatibility.
OpenPGP
OpenPGP is an open-source standard and ecosystem based on the principles of PGP but not tied to any single company or entity. It defines a series of open standards and interoperable implementations for secure email and data communication.
The most well-known open-source implementation of OpenPGP is GnuPG (GNU Privacy Guard). OpenPGP promotes transparency, collaboration, and open-source development, making it widely adopted and trusted. OpenPGP allows users to secure email communications, files, and digital signatures more openly and securely.
Which Security Protocol is Used to Encrypt Email?
We’ve discussed TLS, S/MIME, and PGP — all three are widely used in the email industry.
TLS encrypts emails during transmission between mail servers and email clients, while PGP and S/MIME are both popular options for end-to-end encryption. Most modern email systems use TLS by default, while PGP and S/MIME require additional setup but offer stronger security guarantees.
Are SMTPS, IMAP, and POP3 Secure?
Many people wrongly assume SMTPS, IMAP, and POP3 are security protocols; they are not.
SMTPS, IMAP, and POP3 are fundamental email protocols that support the exchange of emails across the internet. However, these protocols do not inherently provide security mechanisms. SMTPS, though it incorporates a security layer through SSL or TLS encryption, doesn’t enforce encryption universally, leaving email transmission vulnerable without proper configuration.
IMAP and POP3, which are primarily focused on message retrieval, lack built-in encryption, potentially exposing email content during transmission. Users and organizations must implement additional security measures, such as TLS for SMTP, to safeguard emails and ensure the confidentiality and integrity of their messages.
In short, you cannot rely solely on SMTPS, IMAP, and POP3 to ensure the security and privacy of emails, which are as essential as they are in electronic communication.
SPF – Sender Policy Framework
Sender Policy Framework (SPF) is a protocol used to provide security to emails; it helps prevent email spoofing and unauthorized use of your domain names. SPF achieves this by specifying which email servers may send emails on behalf of your domain — this prevents malicious individuals from using your legitimate domain name to send fraudulent or phishing emails.
What is SPF for?
SPF ensures your authenticity and reduces the likelihood of recipients receiving deceptive or harmful emails. By implementing SPF, you can protect your brand’s reputation, enhance email deliverability, and reduce the risk of your emails being falsely marked as spam.
DKIM – DomainKeys Identified Mail
DomainKeys Identified Mail (DKIM) is a critical protocol for secure email communication. DKIM adds an encrypted digital signature to your email messages, which the recipient’s email server verifies. This signature guarantees your email’s content was secure during transit and that it indeed originates from your domain.
What is DKIM for?
DKIM helps prevent email forgery, phishing attacks, and unauthorized modifications to your email content. It enhances email trust and security by allowing recipients to confirm your authenticity, bolstering the integrity of email communications.
This verification process is particularly important for your subscribers, as it helps protect them against malicious and fraudulent emails.
DMARC – Domain-based Message Authentication, Reporting, and Conformance
Domain-based Message Authentication, Reporting, and Conformance, or DMARC, is a protocol that prevents email spoofing and phishing attacks.
What is DMARC for?
This secure email communication protocol allows you to specify an authentication process and define instructions to a server on how to handle emails if they fail authentication checks. This specification can include rejecting, quarantining, or delivering the email as usual.
DMARC also provides reporting mechanisms that enable you to receive feedback about emails that pass or fail authentication, helping you monitor and improve your email security.
DMARC is essential because it enhances the overall security of email communications, protects your brand reputation, and builds trust with recipients. By implementing DMARC policies, you can reduce the risk of cybercriminals using your domain names for malicious purposes, thereby ensuring your emails are more secure, authentic, and reliable.
BIMI – Brand Indicators for Message Identification
BIMI, or Brand Indicators for Message Identification, works in tandem with SPF, DKIM, and DMARC. Its main role is to let you associate your brand logo with your email authentication records.
How Does BIMI Work?
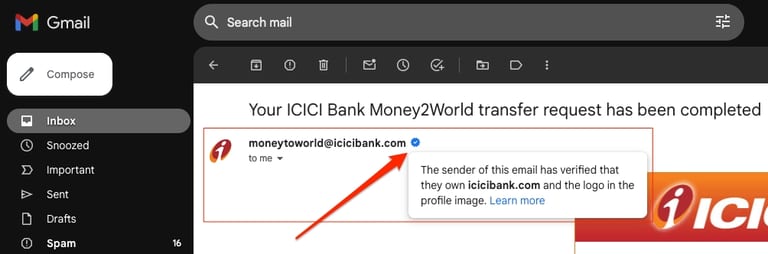
To use BIMI, you have to publish a new DNS email record that includes a URL to your logo. When your emails reach a server, the ESP verifies this association. Once it confirms the email is legitimate, mailbox providers can then display your logo next to the email in the recipient’s inbox. You can see examples if you open up your Gmail Primary inbox.
What is BIMI for?
This security measure is great for email branding plus it assures your readers that no one has spoofed your emails. Note that, in the near future, as BIMI gets more strict, you will need a VMC (Verified Mark Certificate) to prove you own the logo you are using for BIMI.
Which Protocol is Commonly Used to Secure Email Communication?
The three main protocols in email marketing are SPF, DKIM, and DMARC; they work together to create a layered approach to email security and authentication.
While SPF defines authorized sending servers, DKIM adds a digital signature to verify email integrity and authenticity. DMARC wraps things up by allowing you to specify how to handle emails that fail these checks. It also provides feedback to improve your email security.
By using all three in combination, you can significantly enhance the trustworthiness of your emails. BIMI will be joining this trio soon, which is especially important for big brands. Marketers keen on protecting their brand identity should aim to get BIMI-compliant soon.
Which is the Most Secure Email Protocol?
There is no one security protocol that works as well as effectively as SPF, DKIM, and DMARC together.
SPF was the first but DKIM and DMARC followed quickly after, in the early 2000s. Nowadays, email senders and email platforms are expected to have all three security protocols in place, with BIMI implementation to become mandatory very soon.
Mandatory Email Protocols List for Email Marketers
Online threats can be reduced by using this list of security protocols on your domain:
- SPF,
- DKIM,
- DMARC,
- TLS.
FAQ
Which protocol is used to provide security to emails?
TLS (Transport Layer Security) and Secure/Multipurpose Internet Mail Extensions (S/MIME) are commonly used to provide email security.
Which protocol is commonly used for secure email communication?
Transport Layer Security (TLS) is widely used for secure email communication.
What protocol has TXT records that can improve email deliverability?
Both Sender Policy Framework (SPF) and DKIM (DomainKeys Identified Mail) protocols use TXT records to improve email deliverability.
How secure are emails?
With encryption and proper security measures, emails can become highly resistant to interception and phishing.