Email Spoofing Guide: From Panic to Power
Discover essential strategies for recognizing, preventing, and responding to email spoofing. Gain peace of mind with our actionable tips.
Campaign Refinery Team
Email Marketing Experts
What you'll learn
You open your inbox to find an alert about suspicious activity in your bank account. Your heart sinks! The email looks official, and it’s urging you to take immediate action if you don’t want to lose your savings!
It says click on a link to secure your account. Your first instinct is to act quickly.
But something about the email doesn’t feel quite right. The sender’s address; the wording; something is off. So, you pause, step back, and tap into your knowledge about email scams.
Many people face this type of scenario every day. It’s so common that it has its own name: email spoofing. And we’re here to unpack what it involves and what you can do about it.
What Is Email Spoofing?
Email spoofing is a cyber attack where the attacker sends a forged email to trick the user into believing the email is from a legitimate sender.
In other words, the attacker sends a fake email that looks like it’s from someone you can trust.
In that email, they may ask you to:
- Click on a link.
- Download an infected attachment.
- Provide sensitive personal or financial information.
- Transfer money to a fraudulent account.
- Update or confirm login credentials.
- Share confidential company data.
- Follow misleading instructions that compromise security.
- Reply with specific details that can be used for further scams.
An Example of Email Spoofing
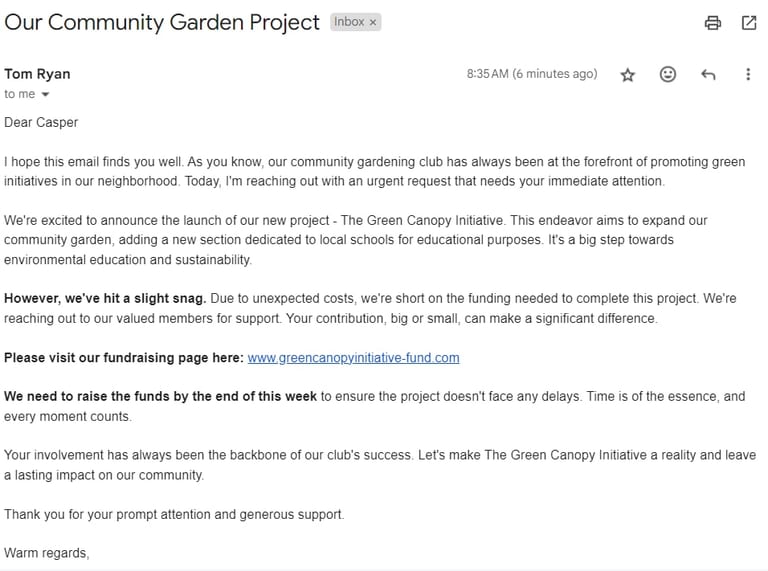
Picture this: You’re part of a local community gardening club. One day, you receive an email that appears to be from the club’s president, someone you’ve exchanged emails with before. The message has the correct name, and it politely asks for contributions towards a new community project.
So, you click the link and make a donation. At the next club meeting, you find out there was no such fundraiser – the president’s email address had been spoofed.
This scammer did their homework. They created an email that perfectly mimicked a familiar and trustworthy source. And now, they’ve at least scammed you out of some money. But they may also have your credit card information!
You might think that this type of attack is too obvious to fool anyone. But it’s happened to even large organizations. A well-known example is when Google and Facebook paid $100 in fake invoices to a guy in Lithuania who impersonated a Taiwanese vendor.
What’s the Difference between Spoofing and Hacking?
Hacking means someone gains unauthorized access to your email account. But spoofing is when someone sends fake emails that appear to come from a legitimate source.
Hacking can completely compromise personal or sensitive data, but spoofing focuses on tricking the recipient into providing information, clicking a malicious link, or initiating an unauthorized transaction.
To protect yourself against hacking, you need:
- Strong passwords,
- Two-factor authentication,
- Email encryption,
- Secure networks.
In contrast, defending against spoofing requires:
- Vigilance in identifying fake emails,
- Educating users about phishing tactics,
- Implementing email verification protocols (more on those later).
Checkout the table below for a summary of the differences between hacking and spoofing:
| * | Hacking | Spoofing |
|---|---|---|
| Definition | Unauthorized access to an email account. | Sending fake emails from a seemingly legitimate source. |
| Objective | Gain control, access, or damage. | Deceive the recipient into providing information or clicking malicious links. |
| Method | Breaching security protocols. | Faking email headers and addresses. |
| Threat level | Completely compromise data and privacy. | Information theft or malware infection. |
| Defense | Strong passwords, 2FA, email encryption, secure networks. | Awareness, vigilance, email verification protocols. |
What’s the Difference between Spoofing and Phishing?
You’ll often hear experts use phishing and spoofing in the same context or even interchangeably. So, it’s easy to assume they’re the same. But they’re two different things, although they can be related.
In simple terms, spoofing is one of the mechanisms used to carry out phishing attacks.
Phishing refers to any attempt to lure victims into clicking on malicious links or downloading harmful apps. Attackers use social engineering tricks to steal the victim’s information, like passwords and banking credentials.
Spoofers send fake emails under the name of a trusted person or business to trick recipients into taking the action they want.
| * | Phishing | Spoofing |
|---|---|---|
| Definition | Deceptive attempts to gather sensitive information. | Disguising communication as from a trusted source. |
| Scope | Broader, includes various communication methods. | Typically focused on email and sender identity. |
| Objective | Obtain sensitive information like passwords or financial details. | Gain trust by impersonating a known source. |
| Method | Deceptive emails, phone calls, websites. | Faking email headers and addresses. |
| Threat level | Can lead to identity theft, financial loss. | Often a part of phishing to initiate trust. |
| Defense | General cybersecurity awareness, caution with unknown sources. | Awareness, vigilance, email verification protocols. |
How Does Email Spoofing Work?
Email spoofers use multiple tactics to lure users into opening a forged email. The attacks range from simple to sophisticated. Let’s explore them in more detail.
Display Name Spoofing
Sometimes, a phony display name is all it takes to deceive an unsuspecting user.
The display name is the name shown to the recipient. Email clients show the name in different locations, like next to the email address or before the subject line.
If you get an email with the display name of a person you know, you’ll be less likely to check if the email address is fake. That’s even worse if you open the email on a mobile app, which has less space to show all the information.
Lookalike Email Addresses
This is a more surefire way to deceive recipients without technical expertise. Instead of — or in addition to — forging the display name, they use an email address very similar to the legitimate domain address.
The address will be almost identical to the original one. For example, they replace the letter “l” with “1” and leave all the other letters unchanged.
In most cases, email recipients don’t stop to check email addresses. So, they easily fall prey to these malicious attacks.
Domain Spoofing
This is a more sophisticated approach, which needs a bit of programming skill. It involves manipulating the email’s headers — technical details about the email, including the sender and recipient addresses.
Many email clients hide away most of the headers to avoid clutter. But hackers can easily exploit headers.
Why?
Because the standard protocol for sending emails (SMTP) doesn’t verify an email’s source.
You can think of this vulnerability as sending a traditional mail with someone else’s return address on the envelope. The postal service delivers the package based on the address on the envelope, without verifying if it actually came from that address.
The attacker manipulates the “From” field in the email header to display a legitimate domain, even though the email is sent from a different source. Since SMTP doesn’t verify the sender, the email appears to come from a credible domain, like a well-known company or a trusted partner.
What Are the Goals of Email Spoofing?
Attackers spoof emails for several reasons, each with its own malicious intent. Here are some of the primary motivations:
Identity Theft
By pretending to be someone you trust, spoofers gain access to your personal information like social security number or financial and tax information. They can use your information to impersonate you when committing other crimes.
They can also use your personal information to open bank accounts or make purchases.
Spoofers can also take over the victim’s social media accounts by asking them to enter their credentials through the spoofed email.
Business Email Compromise (BEC)
This is a sophisticated attack on large businesses where the attacker impersonates a high-level executive, such as a CEO or CFO.
The attacker sends an email requesting an urgent wire transfer with an excuse like securing an important contract, handling a confidential deal, or responding to an emergency.
Employees think the email is a legitimate request from their superiors and transfer the money without request. But the account in the message belongs to the attacker, so they’ll receive the funds.
A Belgian bank was scammed out of 70 million Euros using this exact scenario.
Apart from financial fraud, BEC attacks can also involve requests for sensitive company information. The attacker might ask for payroll data, employee personal information, or confidential project details.
Spread Malware
When an email looks suspicious, you may be less likely to open it, even if it has passed through spam filters. But spoofed emails look more convincing.
If the email contains malicious links, you probably won’t check whether it leads to a legitimate destination. And this is where you’ll get into trouble.
If you’re not careful what you click on, malicious software, ransomware, or viruses, can infect your device and compromise your data.
Get Through Spam Filters
Emails from recognized and reputable domains have a higher chance of passing through spam filters without being flagged. This way, attackers can boost their deliverability rates and target more people.
Avoiding anti-spam mechanisms and regulations is another reason behind spoofing. Plus, some senders pretend to be another sender since their message content violates laws as it contains harassment, blackmail, etc.
Damage Someone’s Reputation
Sometimes, attackers spoof emails to ruin a business or person’s reputation. They impersonate that person or business and send damaging emails in their name. These emails might contain inappropriate or offensive content, misinformation, or controversial statements.
They might carry out this type of attack as part of a larger scheme to sabotage a competitor or public figure. The impact of email address spoofing can be devastating and last for a long time.
Social Manipulation
Scammers may impersonate a famous person to push their own agenda. They can use spoofed emails to manipulate the general public and instill their political or environmental views. The scammer’s goal might be to rally support for a cause, undermine opposing viewpoints, or simply create confusion and discord.
This tactic is effective in manipulating public opinion or spreading misinformation. That’s because recipients are more likely to trust messages that seem to come from a reputable source.

What Happens if You Open a Spoofed Email?
The good news is that your device won’t get hacked or infected if you open a spoofed email. Plus, you can’t tell if an email is spoofed unless you open it.
It’s only after interacting with the email’s content that your data and device can get compromised. For example, after clicking a link or downloading an attachment, you might download malware or get infected with a virus.
As long as you don’t take actions like providing personal information and account credentials, you’ll be generally safe.
How to Tell if an Email is Spoofed
In most cases, spoofed emails are easy to spot. All you need is a bit of caution and mindfulness.
Follow these steps if you suspect an email of being spoofed:
- Don’t click on links. This is the most important step to keep you safe. Before clicking the link, hover your mouse over it and look at the bottom left corner to preview where the link will take you. Triple-check the address to make sure it’s legit.
- Use a redirect tool: If you’re accessing your email through a browser, you’ll probably see googleapis.com when you hover your mouse over the link. That’s not the final stop, though. Instead of clicking to see where you’ll end up, right-click on copy the link address. Then log on to WhereGo.com to figure out where the redirect chain ends.
- Don’t copy/paste links. Type the domain name into your browser to see where it leads. Don’t copy the link address, though, because it might contain URL parameters or lead to a malicious script.
- Don’t download any attachments. It might be a simple PDF or zip file, but attackers can hide malware or ransomware inside these files. Once you open the attachment, the malware will execute in the background, and you’ll only find out when it’s too late.
- Check the sender’s information: Most spoofed emails have fake addresses in the “From” section. Check the sender’s email address and display name to make sure they match. Pay attention to spelling mistakes.
- Read the message carefully. Look for poor spelling and grammar or generic greetings (like “Dear Customer”). If the message asks you to do something urgently, don’t do it. By creating a sense of urgency, scammers prevent you from thinking clearly.
- Look for inconsistencies. Inspect the telephone numbers, signatures, or physical addresses. For example, if the physical location and the area code don’t match, the email is likely forged.
- Verify using another channel. For example, if an email seems to be from your bank and wants your personal information, don’t take action immediately. Call your bank and ask if they sent you such an email. Similarly, double check requests for wire transfers or confidential company information with your superiors.
What To Do if You Get a Spoofed Email
If you’re (almost) sure that an email you received is spoofed, follow these steps:
- Report the email: Forward the suspicious email to the IT department if you’re in an organization, or report it to relevant authorities or services, like your email provider. If you’re on Gmail, click on the icon with the three vertical dots. Then select “Report phishing.”
- Submit it on PhishTank: PhishTank is a free community site where users can submit suspected phishing emails. Users then check and vote on whether these submissions are part of known phishing campaigns. You can also search the database using the URL in your suspected message.
- Mark as spam: Mark the email as spam or junk in your email client. This action helps your email provider improve spam filtering.
- Delete the email: Once you’ve verified that the email is indeed a spoof and reported it, delete it from your inbox to avoid accidentally clicking on it.
- Update your security software. You should always have an up-to-date security suite installed on your device. Antivirus software can detect malicious emails and warn you against them if you click on a link by accident.
Is Email Spoofing Illegal?
Spoofing can be illegal depending on the damage it causes and the specific laws in each jurisdiction.
Different countries have different regulations for cybercrimes. Some regions have strict laws for spoofing email addresses, while others consider it under digital fraud or identity theft laws.
In general, creating an anonymous email address or modifying email headers isn’t illegal on its own. But it becomes illegal if someone uses these for harmful, deceptive, or fraudulent purposes.
For example, phishing attacks, which often use spoofed emails, are illegal because they obtain personal information or transfer funds under false pretenses.
If email spoofing is used to distribute malware, it can be a cybercrime. Laws, like the U.S. Computer Fraud and Abuse Act, criminalize unauthorized access to computers and networks. They also ban the “transmission of a program” that causes damage to a computer.
Email spoofing can also lead to civil legal consequences. If an organization or individual suffers financial losses or damage to reputation, they might seek damages through civil litigation, which might fall under the jurisdiction of the Federal Trade Commission. This is especially with BEC attacks.
How to Protect Your Business Against Spoofing Attacks
Safeguarding your business against spoofing attacks requires a combination of technical details and employee education. Here are a few measures to consider:
Implement Domain Authentication Protocols
Domain authentication protocols verify that an email claiming to be from a domain genuinely originates from that domain. They’re key tools in fighting email spoofing and provide a layer of security.
Here’s a breakdown of the three main protocols:
- Sender Policy Framework (SPF): This protocol lets the domain owner specify which email servers have permission to send emails on behalf of their domain. When an email server receives an incoming message, it checks the SPF record in the DNS to verify if the email came from an authorized server. If the check fails, it could indicate spoofing.
- DomainKeys Identified Mail (DKIM): DKIM adds a tamper-proof signature to the message to validate its domain name. It uses a pair of keys, one private and one public, to sign and verify emails. The sending server signs the email with a private key, and the receiving server uses the public key, published in the DNS, to verify the signature. If the DKIM signature is valid, it means the message didn’t get altered in transit.
- Domain-based Message Authentication, Reporting and Conformance (DMARC): With DMARC, domain owners can indicate that their emails are protected by SPF and/or DKIM. It tells the receiving mail servers what to do if neither authentication method passes – such as rejecting the message or sending it to the spam folder. DMARC includes sophisticated reporting features.
These mechanisms are so important for sender reputation that we require all our clients to implement them from the first day they join us. Not only are they a good security measure, but they’re also a sign that you’re a legitimate business with no intention to send spam.
Sign Up with an Email Security Provider
These providers specialize in delivering advanced security solutions for email protection. Their services typically include real-time scanning for spam, phishing, and malware. They also offer sophisticated filtering algorithms to detect and prevent email spoofing and BEC attempts.
Email security providers have machine learning algorithms trained on vast datasets of legitimate and malicious emails. They analyze various email attributes, such as header information, sender behavior, and writing style, to detect spoofing.
Educate Your Employees
Hold a training session to educate employees about the risks of email spoofing. Teach them how to recognize signs of a spoofed email, such as mismatched email addresses and suspicious links or attachments.
Emphasize the importance of double-checking email content, especially for requests that seem out of the ordinary.
How to Detect Spoofed Emails Using Email Headers
Email headers contain detailed information about the sender, the email’s journey through the internet, and how it arrived in your inbox.
They’re the most surefire way to check whether an email is spoofed. But because they’re a bit technical, we saved them for last.
Let’s go over how to use them to identify potential spoofing.
First, you need to access the headers, and the method varies from one email client to another. Here’s how to do it with the most common ones:
How to View Email Headers in Gmail
If you’re using Gmail on your web browser, follow these steps:
- Click on the suspected email to open it.
- On the top right corner, click the icon that looks like three vertical dots.
- Click “Show Original.”
- Scroll down to see the relevant fields.
If you’re on a mobile device, the official Gmail app doesn’t offer a way to check email headers.
So, you have two options:
- Log on to your gmail via your mobile web browser and load the desktop version (recommended).
- Use an advanced email app such as K-9 (not recommended if you’re not tech-savvy).
How to View Email Headers in Outlook
If you’re using the Outlook app on your computer, follow these steps:
- Double click the message whose headers you want to view.
- Navigate to File > Properties.
- Find the header information in the Internet headers box.
If you’re using the web version, open the message. Then click the ellipsis icon on the top and choose View message source.
How to View Email Headers in Apple Mail
The Mail app is probably the easiest one to view headers.
Simply, choose View > Message > All Headers. That’s it.
Analyze Email Headers
Once you’ve accessed the headers, look for these fields:
- Return-Path: This should match the sender’s email address in a legitimate email. Otherwise, it can be a red flag.
- Received From: This shows the email’s journey. If the email claims to be from a known domain but the path shows different or suspicious domains, it could indicate spoofing.
- From: Although it’s easy to spoof this field, inconsistencies or unusual formatting here can also be a sign of a spoofed email.
- Reply-to: If this field is different from the sender’s address, replies are redirected, which could be a sign of malicious activity.
- IP Addresses: If you really want to dig deep, you can check whether the IP address listed in the “Received From” header matches the legitimate sender’s IP. Tools like WHOIS can help in this verification.
Check for Domain Authentication
Domain owners can configure their DNS email records to prevent email spoofing. Domain authentication is a process that proves an email actually originates from the domain it claims to be from.
There are three domain authentication protocols to check for: SPF, DKIM, and DMARC.
We’ll talk about these protocols later, but for now, make sure the email passes at least one and preferably all of these tests.
Also, note that the domain owner is responsible for implementing these protocols. As the recipient, you can only check whether the domain is authenticated.
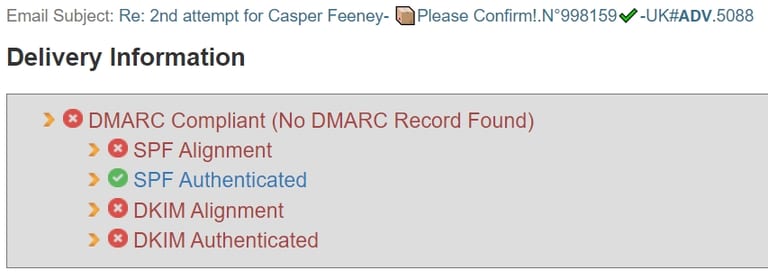
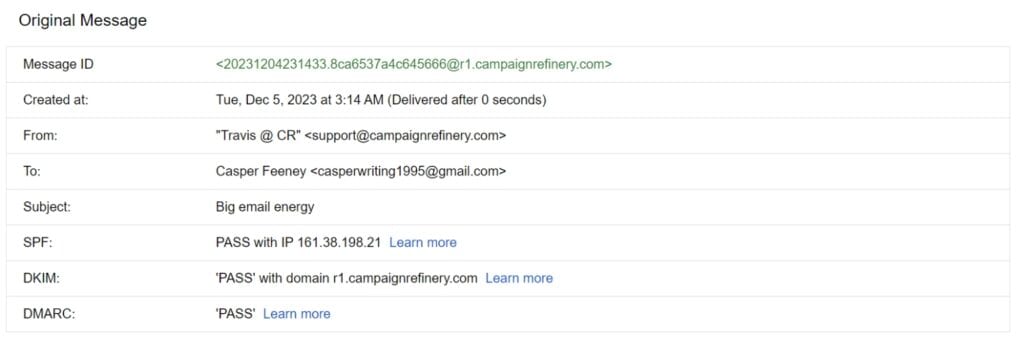
Here’s a screenshot of an email sent from our domain. As you can see, the message passes all three domain authentication protocols.
Use an Analysis Tool
The tips so far should be more than enough to protect you from spoofed emails.
But if you really want to get to the bottom of a message you received — or if you just want to geek out — here are a couple of tools to try:
- MxToolBox Header Analyzer: Email headers are indecipherable in plain format. This tool will make them easier to digest. Copy/paste the email header you want to analyze, and it’ll generate a nice-looking page where you can find all the information you need.
- Google Message Header Analyzer: This is a similar tool with a clean interface, which will extract the email’s journey from the header. It’s useful if you want to see where a message originated from.
A Practical Example of Detecting a Spoofed Email
While writing this piece, it occurred to me to look inside my spam folder. And sure enough, the first message was a spoofed email trying to convince me to click on a link because I had “won” a reward.
Here’s what the email looked like:
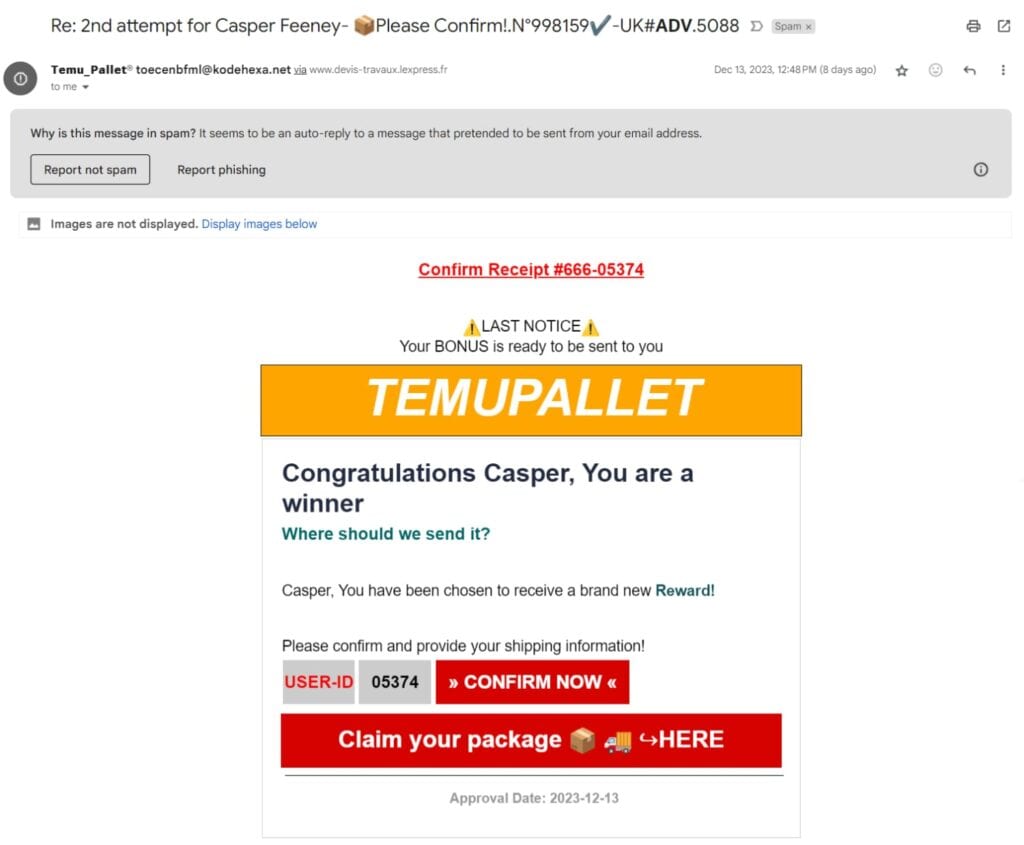
When you look at the message, you can notice a few things:
- It tries to create a sense of urgency by making it look like this is the second time they’ve contacted me. It wasn’t. I checked.
- The “LAST NOTICE” header enforces that sense of urgency.
- They added two random numbers to make the email seem more legit.
And They Were Sneaky …
They coded the HTML in a way that the entire email was a link. So, no matter where I clicked, I’d end up where they wanted me to.
Be extremely careful where you click if you receive an email from someone you don’t know.
Down the Rabbit Hole
I first wanted to know where the link would send me if I clicked on it. So, I copied the address and pasted it into WhereGoes.com. Here’s what I got:
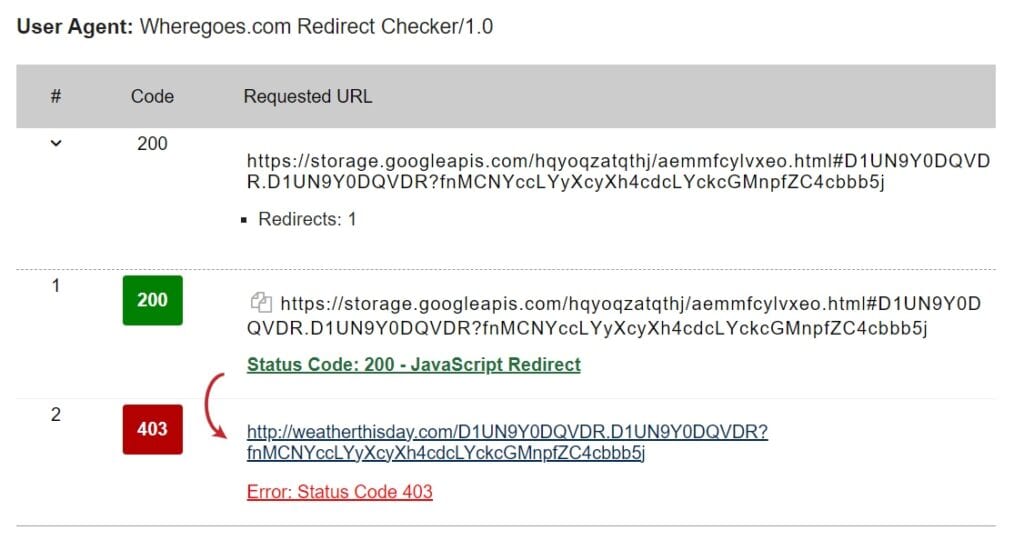
The 403 error means the attackers were clever enough to prevent bots from accessing their page.
So, I opened the link on a virtual machine, which was disposable and isolated from my main operating system. After being redirected five times, I ended up on a casio website. Too bad I didn’t get that reward!
Checking the Headers
Now, let’s check the headers to confirm what we already know.
Out of the three domain authentication protocols, this email only passes one. But there’s a catch: SPF alignment didn’t pass.
That means the email addresses in the “From” and “Return Path” headers didn’t match — a classic sign of a spoofed email. The only reason that the email passed SPF was because the address in Return-Path was correctly configured for the protocol.